"In cybersecurity, time is the enemy — and AI is how we fight back."
Every second, the digital world faces a growing wave of cyber threats. From phishing scams and ransomware attacks to advanced persistent threats (APTs) and insider risks, organizations are under constant siege. Traditional security tools—built on static rules and manual monitoring—can't keep up with the evolving tactics of modern cybercriminals.
Enter AI-powered threat detection, a transformative approach that uses machine learning (ML), behavioral analytics, and automation to detect and neutralize attacks in real time.
In this article, we'll break down how AI-driven threat detection works, explore the key technologies behind it, and show why it's becoming the cornerstone of next-generation cybersecurity.
1. The Cybersecurity Challenge
Global cyberattacks have increased by more than 30% year-over-year, with financial damages surpassing $10 trillion annually by 2025. The growing complexity of IT environments—spanning cloud, IoT, and remote networks—has created an attack surface too vast for traditional defenses.
🧱 Limitations of Legacy Systems:
- Signature-based detection (identifies known malware patterns only)
- Rule-based alerts (manually configured)
- High volume of false positives
2. What Is AI-Powered Threat Detection?
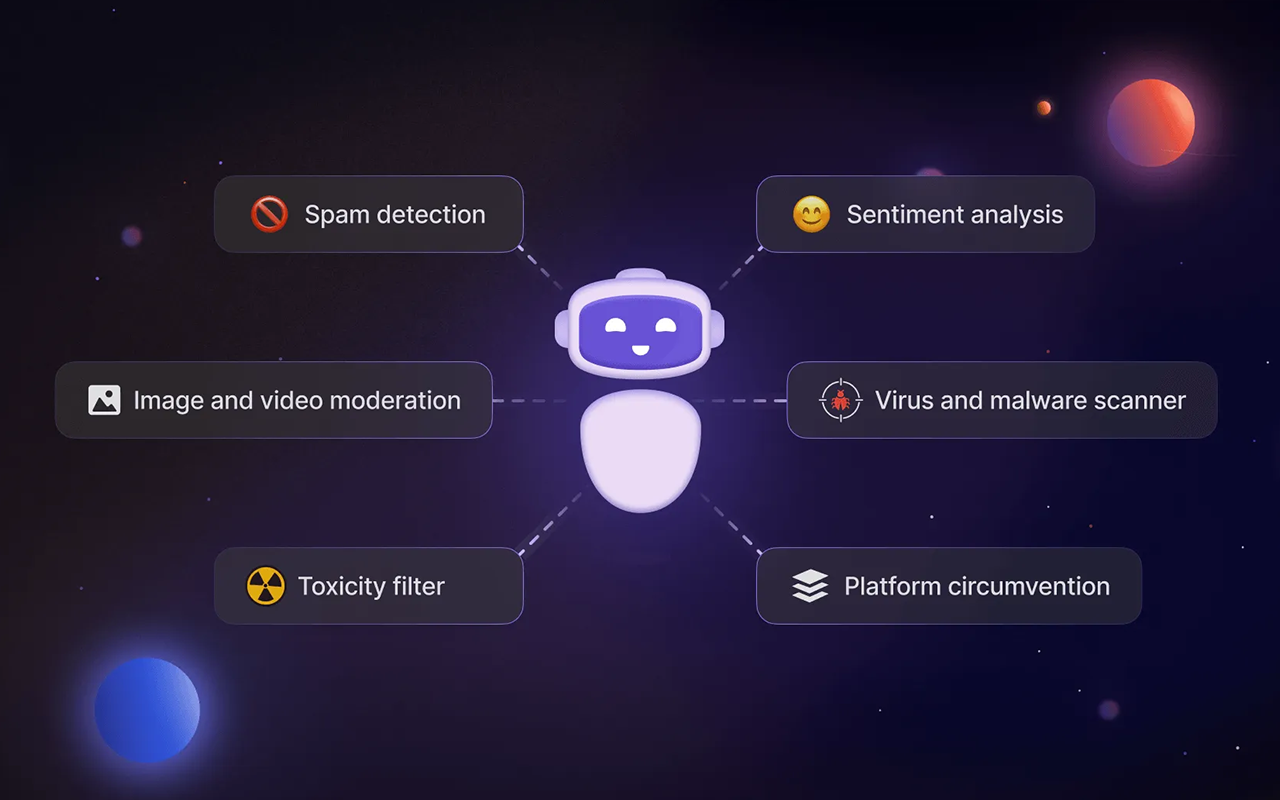
AI-powered threat detection leverages machine learning algorithms and data-driven analytics to automatically identify malicious behavior, even if it's never been seen before.
💡 Definition: AI-powered threat detection is the use of artificial intelligence and machine learning to analyze data, identify anomalies, and detect potential security threats autonomously.
3. How AI Detects Threats: The Core Process
At its heart, AI threat detection works through a multi-layered process of data collection, analysis, and response.
- Data Collection: Gathering raw data from network packets, endpoint devices, and cloud platforms.
- Feature Extraction: Converting raw data into meaningful patterns and behaviors.
- Anomaly Detection: Identifying deviations from normal patterns (unusual login times, data transfers).
- Threat Classification: Classifying detected anomalies as benign or malicious.
- Response and Mitigation: Automatically triggering alerts, quarantining actions, or firewall updates.
4. Machine Learning Techniques in Threat Detection
AI-powered systems use a variety of ML techniques to improve accuracy:
- Supervised Learning: Trained on labeled data for malware detection and intrusion classification.
- Unsupervised Learning: Detects unknown or novel threats like zero-day exploits.
- Deep Learning: Neural networks for detecting complex relationships in encrypted traffic.
- Reinforcement Learning: AI agents that dynamically adapt firewall policies.
5. Behavioral Analytics (UEBA)
User and Entity Behavior Analytics (UEBA) models typical behaviors for users and devices. When deviations occur—such as a finance employee downloading gigabytes of data at 3 a.m.—the system flags it.
⚙️ How It Works: Tracks logins, file access, and connections to build behavior baselines and score risks in real-time.
6. The Role of AI in Network Traffic Analysis
AI enhances NTA by processing vast amounts of real-time data to identify subtle signs of intrusion:
- Flow-based monitoring for unusual communication.
- Protocol analysis for malicious payloads.
- Graph learning to identify lateral movement.
7. Real-Time Anomaly Detection
Anomaly detection lies at the heart of AI threat intelligence. By establishing baselines for metrics like login frequency and network latency, the system identifies unusual patterns in milliseconds.
"AI doesn't sleep. It detects threats 24/7, even when your team can't."
8. Integrating AI into Security Infrastructure
AI-powered threat detection enhances existing systems like:
- SIEM: Enriches alerts with contextual insights.
- SOAR: Automates incident response playbooks.
- XDR: Extends detection to endpoints and clouds.
9. Key Benefits
- 🚀 Speed and Efficiency: Detects threats in seconds.
- 🧩 Reduced False Positives: Minimizes alert fatigue.
- 💬 Detecting Unknown Threats: Identifies zero-day vulnerabilities.
- 🔒 Scalability: Scales across hybrid and multi-cloud environments.
10. Challenges and Limitations
While powerful, AI threat detection faces challenges like data quality, model explainability ("black box" models), and adversarial AI where attackers use AI to bypass defenses.
11. Conclusion: The Future of Cyber Defense Is Intelligent
AI-powered threat detection is not a luxury—it's a necessity for the digital age. By combining automation and analytics, AI empowers organizations to stay ahead of attackers.
✅ Key Takeaways
- AI uses ML and analytics to identify cyber threats in real time.
- It analyzes network, endpoint, and behavioral data to detect anomalies.
- Benefits include faster detection, reduced false positives, and adaptive learning.
- The future points toward autonomous and self-healing cybersecurity.